TLS configuration (TLS versions, ciphers) is one of the most important security settings, given that SSL/TLS 1.0 is almost 20 years old at this point and full of vulnerabilities. TLS 1.2 is the current de-facto standard, TLS 1.3 has been approved earlier this year and it is quickly gaining momentum.
TLS configuration in DataPower is doubly important since DataPower is typically used as the gateway for the traffic from public Internet.
DPBuddy allows for defining TLS configuration policies. These policies can be easily applied across multiple devices and domains.
It also allows for quickly querying (and comparing) configuration of DataPower objects, including the TLS-related ones. DPBuddy consolidates configuration settings from multiple DataPower gateways in a single report.
The key TLS-related object types in DataPower are SSL client profile and SSL server profile.
This is how you can set the TLS version across multiple devices and their domains:
dpbuddy updateConfig -objects "SSLClientProfile, SSLServerProfile" -updates "Protocols:{TLSv1d2:on}" -domains "domain1, domain2" -device "dp1, dp2"
You can find more information about the “updateConfig” command in our documentation.
DPBuddy 3.5 (to be released soon) also allows for specifying all of the domains, irrespective of whether a domain contains an object of a given class:
dpbuddy updateConfig -objects "SSLClientProfile, SSLServerProfile" -updates "Protocols:{TLSv1d2:on}" -domains ".*" -device "dp1, dp2"
Multiple TLS versions can be enabled as well:
dpbuddy updateConfig -objects "SSLClientProfile, SSLServerProfile" -updates "Protocols:{TLSv1d2:on, TLSv1d1:on}" -domains "domain1, domain2" -device "dp1, dp2"
The versions that are not explicitly mentioned out in the “updates” parameter will be disabled.
The “updates” parameter is really flexible, you can provide several settings at once. The names of the settings must match the element names in the exported DataPower configuration.
For example, you can update both ciphers and the TLS version:
dpbuddy updateConfig -objects "SSL.*Profile" -updates "Protocols:{TLSv1d2:on, TLSv1d1:on}, Ciphers:[ECDHE_ECDSA_WITH_AES_256_GCM_SHA384,ECDHE_RSA_WITH_AES_256_GCM_SHA384]"
(Updating ciphers requires DPBuddy 3.5, all the other elements supported in 3.4)
DPBuddy 3.5 also allows you to define your TLS settings in dpbuddy.conf (or in a different config file included into dpbuddy.conf):
sslConfig: {
Protocols:{TLSv1d2:on, TLSv1d1:on},
Ciphers:[ECDHE_ECDSA_WITH_AES_256_GCM_SHA384, ECDHE_RSA_WITH_AES_256_GCM_SHA384]
}
You can then reference this configuration from the “updatedConfig” command
dpbuddy updateConfig -objects "SSL.*Profile" -updateConfPath "sslConfig"
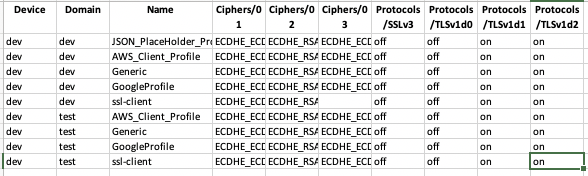
DPBuddy provides extensive reporting capabilities allowing you to view all of your TLS settings in one place:
dpbuddy configReport -domains ".*" -toDir confReport -objects "SSL.*Profile" -excel
In DPBuddy 3.5 you can also specify what elements to include/exclude into the report:
dpbuddy configReport -includeElements "Protocols.*,ciph.*" -domains ".*" -toDir confReport -objects "SSL.*Profile" -excel
Here is the output of the report (in Excel format):
More information about “configReport” is available in the documentation.
Automate without scripting, monitor your services, check for compliance
Realize full potential of DataPower gateways